|
Note: you can use the search button above which looks like |
|||||
|---|---|---|---|---|---|

|
got a virus? |

|
|||
PC Technician computer tips and help
|
|
Check out computer performance - my computers HERE
| PC Technician Help and Tips | |||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|

|
 How to install dual boot - Windows 8 and 7
How to install dual boot - Windows 8 and 7
 Nasty hacker unicode exploit
Nasty hacker unicode exploit
 hard drive backup and recovery solution
hard drive backup and recovery solution
 Printer doesn't print - possible solution
Printer doesn't print - possible solution
 Internet Explorer unstable? - Try this
Internet Explorer unstable? - Try this
 Cannot print web page from IE9 - Try this
Cannot print web page from IE9 - Try this
 Recover damaged user profile windows XP
Recover damaged user profile windows XP
 GAC_32/Desktop.ini trojan - removal
GAC_32/Desktop.ini trojan - removal
 Avast antivirus - Problem uninstalling?
Avast antivirus - Problem uninstalling?
 Snipping Tool Windows 7 - screen capture
Snipping Tool Windows 7 - screen capture
 How to get rgb values from an image
How to get rgb values from an image
 More Tips and Help - Continued
More Tips and Help - Continued
|
||||||||||||||||||
|
|
|||||||||||||||||||
|
|||||||||||||||||||
| Monthly tips from the PcTechnician - also, check the ARCHIVE | ||
|---|---|---|

|
Beware of fake BBB email
This month's tip has to do with a bogus email from the Better Business Bureau. I actually got this email and it claims that a complaint has been filed against me. The email wants me to open a complaint report - Yeah sure! Like I am going to open some file - NOT! You can click HERE to see a copy of this bogus email. |
|
 MORE INFO ABOUT COMPUTER VIRUSES
MORE INFO ABOUT COMPUTER VIRUSES
 MORE ANTI-VIRUSESRMATION
MORE ANTI-VIRUSESRMATION
|
Some thoughts on solving virus problems Short Background: My computer career started about about 46 years ago. The first computer I worked on was an IBM 7094 - I wrote a Fortran program to find the inverse of a matrix to teach myself programming. This landed me a job as a Fortran programmer - since nobody (relatively speaking) had experience with Fortran. Since then I remained in programming from Fortran, Cobol, PL/1, etc on mainframes to the PC. I have been repairing, building, etc. PCs for about the last 20 years. Mostly, I now "fix" computers by removing viruses, malware, etc. I usually advise my clients to buy a new machine if they have serious hardward problem - since the cost of a PC has dropped dramatically over the last few years. Since most virus behavior varies wildly - I don't use the same protocol to remove a virus. So here are a few things I try to do CONTINUE... |

|
Why is the reported physical usable memory ( RAM)
less than the actual installed memory in windows 7 ? There is not a simple explanation for the difference. But I will try to summarize as best as possible. According to microsoft, the usable physical memory available for your computer is the total physical memory minus memory that is reserved by the hardware. For example, a video adapter that has 1 gig of onboard memory has this memory "mapped" to the computer's RAM memory thereby making this 1 gig of physical memory unavailable for the operating system and your applications. Another factor is the motherboard. The chipset on the motherboard must be able to support more address space ( probably by a factor of 2 ) than the total installed physical memory. A third factor is the version of windows 7 that is installed , ie , 32-bit or 64-bit. CONTINUE... |
|
Artificial Intelligence - Is it a fraud and a Sham? Well, it's been many years now and the promise of artificial intelligence ( AI ) still seems to be about where the promise of controlled fusion is currently - nowhere! All the talk, both past and present, about the benefits humans would reap from this pursuit still seems elusive as ever. I remember, back in the 60's, while working in a lab, how excited me and my colleagues were when we got our first computer - it was an IBM7094. One member of our group "discovered" a program that would "learn" how to play tic-tac-toe. This was exciting stuff - a computer would actually "learn" to do something. Sure enough, the program would lose the first several games against humans but eventually it "learned" to play at a level such that it would consistantly play to a draw. Upon analyzing the program, it turned out that all the program was doing was storing a history of moves and categorized the moves that would lead to a loss. Eventually, it had enough games stored so it would no longer lose. What a disappointment! This was not learning as one would intuit learning to be. CONTINUE... |

|
|
||||||||||
Are you Suspicious of a Web Site as being dangerous?
Then enter domain (eg, name.com ) in the box below:
![]()

|
|
|
What's the Code?
Recently, I did a project in Visual Studio Basic for a friend. This is an inventory control and reporting system for an antique store. I have some code examples from this project which may be of some help to some of you. These examples will read an MDB database and extract some values and save them to a text file. The code illustrates the following: 1. Access an MDB database using a connect string. If you have ever tried this - it can be painful as the varying syntax levels may drive you to drink - see link HERE 2. Replace characters in a string. 3. Replace null values. 4. Write to a text file. CONTINUE.... More Code Examples Below:  Make global changes to files in a unix directory structure
Make global changes to files in a unix directory structure
|
|
|
Oh Microsoft, how do I love thee ..... let me count the ways. Well, not really. I admit that, I have been in the microsoft camp ever since its inception and somehow missed getting on the Apple express. And yes, I am sure the Apple dumpling gang would be able to count the ways they love their Macs. I can easily understand why Mac users love their Macs. MSDOS was intimidating to anyone new to computers, although I felt right at home using command line prompts as I came from a mainframe background ( IMB360's ) and TSO - ie, Time Sharing Option to connect to the mainframe. CONTINUE... |

Oh No! My excel and word documents are damaged - Now what? Don't worry - just click on one of the links below! |
|

|
|

| |
 COMPUTER GAMES AND CONSOLES
COMPUTER GAMES AND CONSOLES |
|---|
|
Play high end games on an Alienware laptop computer |

|
Help with HTML --- Pick one:  HTML color code translation
HTML color code translation  HTML codes for special symbols
HTML codes for special symbols  HTML codes for special characters
HTML codes for special characters
 Make 2 columns even length using CSS and DIV tags
Make 2 columns even length using CSS and DIV tags
 RESET Help Box
RESET Help Box
|

|
How to translate a foreign language web page
to English
Sometimes when browsing the internet you may come across a page that is in a foreign language. The page may have a translate button to press and the page is quickly translated but what do you do when there is no button? This happened to me and the page was in Russian - so here's what I did to get the translated page... CONTINUE |

|
How to handle a file with no or an unknown extension
Unlike the file names in Macintosh or unix, Microsoft decided to add extensions to the names of files so they could be associated with the application that created them. This was done, so when you double click on a file - windows will open (read) the file with the correct application that created it. CONTINUE ... |

|
How NOT to make money on the internet.
Where do I start? I have tried to make a few bucks on the internet over the last 8 months and all I found out that it is almost impossible for a variety of reasons. I think that the magnetic draw to making money on the internet is the volume of potential visitors. Sure, if I can get about 300 unique visitors a day - that ought to do it! Well, reality sets in pretty quickly - as I tried to figure out how to build traffic. CONTINUE ... |
|
I used to care but things have changed |
Dedicated to My Old Pal Google
This music is dedicated to my old pal Google. In appreciation for cutting off my adsense account. Thanks. Respectfully, PCT Okay, somebody didn't like my sarcastic music choice and sent me the following: What pitfalls to avoid if you are using Google Adsense to make money on your website From: A Contributor Google Adsense has always been the main income source for many people who have high traffic on their websites. There are lots of money that can be made in this business, and those who plan to use this as an income source need to know about the Do's and Don'ts in order to achieve success with this method. The truth is that many marketers make thousands of dollars almost everyday with Google Adsense. The only reason why so many people fail is because they don't do what's right for their campaign. CONTINUE... |

|
Well, That's Odd - Bizzare quirks in Windows
I recently came accross some odd facts about Windows. It appears that you cannot create a folder or file with the name "con" and it has been reported that Microsoft could not give a reason why this should happen. I tried to do this using both a window interface and a command prompt. I also tried to rename some file ( called it con1) to "con". No dice - you cannot do it. The next oddball has to do with the Notepad program - Open notepad and type in the following ( exactly as shown - the "B" is uppercase): Bush hid the facts Now save this into a file (give it any name you want ) and re-open it. The text now looks like it is chinese and MS could not explain this either. It will work correctly if you make the "B" in Bush lower case, or if you change any other letter to uppercase. Now, that's odd! |
|
Fonts, fonts, fonts - my kingdom for a font
In my mind's eye I could see a font that I thought would be of interest. I wanted something that looked like tubes or pipes. So I went on a quest to find such a font - and in the process I learned more about fonts than I wanted to - and then decided to document my findings at pc technician. Hopefully this info will prove useful for some of you .... CONTINUE |

|
Convert a string to a MD5 Hash value |
|
Get the number of Google indexed
pages for your domain |
|---|
I've suffered with tinnitus for 50 years so I plan to buy one of the sound file downloads given below. I've tried some rememdies but none really helped. My tinnitus sounds more like a whooshing than a ringing in my ears. This is my last attempt as I don't think there is a "real" cure yet.
 |
|
| THE GEEK SIDE | |
 Adsense is NonCents
Adsense is NonCents
This space was formerly reserved for my Adsense ads. But google cut off my account just before my first paycheck (they kept the money) - without any warning or any real explanation except some vague nonsense that my account "poses a risk of generating invalid activity" So I filed an appeal to have my account re-instated. This was a waste of time as the appeal was denied. I still do not understand what the problem was. Okay - so now I can put any link ( no CTR fee ) without worrying about their TOS. Some belong to friends and are free. Mouse over the links for thumbnail web site view. |
|
|
· Play free casino games - fun  · Baja TV - fantasic videos  · Why not date a rich man?  · Pianist, vocalist - Eastern Long Island  · 420 dating site  |
|

| My customers rave about these two tablets from Toshiba. In fact one customer bought 3 of these for his lawn care business and uses one of them to link up to the office computer ( using GoToMyPC software ). | ||
Translate Page:
|
Buffon Needle Problem - Computer Simulation
One can calculate the value of π by dropping a needle of length k onto a grid of parallel lines whose length is greater than k. The value is determined as the probability of hits (the needle crosses a grid line) to the total number of tosses. This value is π = ( 2 * k * total-tosses) / (number-of-hits). This calculation was simulated with a computer program. The program was run on several platforms and processors. I ran the simulation for 10 million tosses and a needle length of .8. I assumed the grid lines to be one unit apart. ...see results.... |
|
Simulation - Normal Distribution Watch the balls drop - produces bell-shaped curve Click on image to stop - when bored click here for more on simulations. if you don't see the applet run - then check this PAGE |
|
Math can be fun Can 1919 be represented as the sum of a cube and a fourth power? ANS: Click on bookworm for answer and more |
|
|
As I was trying to solve this problem, I started to think
tangentially about how would I be able to get the last five digits
using a computer program written in basic. Using double
precision , ie, 64 bits to get the result would not do it. Since
only 52 bits are involved in expressing the "precision". The
other 11 bits are used for the exponent. Well, 252
can only give a precision to 16 places - not enough. Using double
precision interger arithmetic does not do it either - only 10 places.
So I investigated the ways to do high precision numerical
calculations. I stumbled across this ARTICLE. Yikes! More than I could handle. So, just for
laughs I tried the windows calculator and lo and behold and dipped
in butter fat, I got the full answer - try it. Also try to do 2128
to see the number of places that can be expressed ( the upper limit
- about 32 places) Obviously, a high precision alogrithm is used in
the calculator - and this is how I get my kicks. By the way the
breakoff point ( where the result is displayed as an exponent )
is somewhere between 2 106 and 2 107.
Quick son - get the Prozac.
OR - click HERE to view videos on mathematics. |
|
Fun with Biology I never really got to study biology. As a boy I started out with chemistry and my fascination lead to all kinds of dangerous experiments. In those early days, you could walk into a chemical supply house and buy really dangerous stuff. The only exception was concentrated acids. It was a good thing I couldn't get those acids as I wanted to make guncotton - probably saved my life. My interests then shifted to physics and mathematics and then one day I read a book by Erwin Schroedinger - called "What is life". Schroedinger is the physicist who developed the equation that describes quantum mechanical behavior. In the book, he ponders the question of what is life and in an apologetic manner ( since he is a physicist and not a biologist ) questions how a virus can actually express the attributes of a living system. Since a virus is composed of approximately several hundred thousand molecules, then how is it that the virus can behave the way it does. The relatively small number of molecules cannot act, statistically speaking, the same way as a living cell like a human cell which has about 10 trillion molecules. Schroedinger then made the case that a virus must do what it does by playing by the rules of quantum mechanics. I then got lost in his analysis and decided to view biology on a more rudimentary level and to just enjoy the wonderful and strange facts from biology which can be found HERE . |
>
|
Fun with your Photographs |
| I found two programs that manipulate photographs to give some interesting results. One program is actually an online web site where you can upload a photo ( of yourself ) and turn it into a cartoon image. You can upload the photo from your computer or from a url. Once uploaded - the program "cartoonizes" the photo and in about 30 seconds - it is displayed for you to download. The result looks great and a second benefit is that it is absolutely free. You can try it yourself HERE. The second program is a free download. This program called "FotoSketcher" will take an image and turn it into a painting. The program has a nice user interface and a lot of assorted effects to transform your photo. For example, it can produce sketches in oil or pastel, pen and ink, oil painting with several types of painting effects, and some other stylized effects. I liked this program so much I sent the author some coffee money - (as he put it ) as a donation. Well, I sent him enough money to buy a couple of Starbucks coffees. You can get the program HERE. |
>
>

|
|
Free Wallpaper
We have some photos that you can use as wallpaper. Just click on a link below - when image is shown - right click on the image and click on "Set as Background". This image should now be your desktop background. |
|
· Hawaiian beach
· Hawaiian Cliffs · Country scene · Fireworks · Fountain · Halloween · Moon · Country road · Shield · Hawaiian stream · Country stream · Grand Canyon · Grand Canyon Window · Bryce Canyon |
|---|
>
 Need to chill out?
Need to chill out? Then click on surfer. |
|
|---|---|
| Some facts + LSNED (Learn Something New Every Day) | |
| Archive-LSNED | |
| Strange Biology Facts | |
| Terrific Fractal Art |
| Fun with Physics | |
|
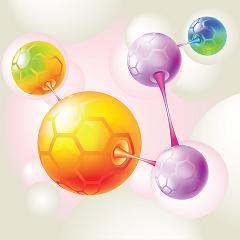
In case you missed it - the world of physics is on the threshold of important
particle physics discoveries. In Geneva, Switzerland a particle accelerator
called the Large Hadron Collider (LHC) is now operating at about half of
its full power. The LHC collides beams of protons together to "see" the
constituents of protons. It is hoped that these experiments will provide
some answers to the fundamental nature of matter. One such quest is
to determine the existence of the Higgs boson. The so-called god particle
which according to theory - gives mass to the known particles. So the
Higgs particle and its associated field gives mass to all particles which
includes the proton - the building block of matter. The theory of particles
is called QCD ( Quantum Chromodynamics ) and recently, physicists have
used this theory with some approximations to create a computational
framework in which to calculate the mass of the proton. So, from
first principles a basic constant of nature , ie, the mass of the proton
was calculated using supercomputers. These computations would
not be possible without the computer. So, by performing an enormous
number of calculations the mass was determined. You have to understand
the components of a proton ( quarks, which have a mass total less than
the proton and gluons, which are massless) cannot just be added up
to get the mass of the proton. In fact, these calculations say that even if
the quark masses vanished, the proton mass would not change much.
Now that's computing. The interior of a proton is a bee-hive of activity
with the gluons and quarks interacting like crazy and for computers
to unravel this mess - is truly amazing. To summarize, using QCD and
assuming zero mass for the quarks, and zero mass for the gluons, and
that space is not continuous but a grid like structure and allowing
the grid points to approach zero and of course a supercomputer -
the mass of the proton was calculated to within 10% of its measured value!
Now put that in your pipe - Einstein (who by the way did not accept quantum mechanics or at least thought that it was an incomplete theory) See a pictorial representation of the interior of a hadron (image below). If you aren't bored out of your mind yet - then see more on particle physics HERE. |
|
 The interior of a hadron, such as the proton or neutron, is not static. Gluons fluctuate in a collective
fashion, illustrated by the red-orange-yellow-green-blue fluid. Sometimes the gluon field produces extra
quark-antiquark pairs; here, a proton (uud) has fluctuated into a ? hyperon (uds) and a kaon (u).
CREDIT: D. LEINWEBER/CENTRE FOR THE SUBATOMIC STRUCTURE OF MATTER, UNIVERSITY OF
ADELAIDE
The interior of a hadron, such as the proton or neutron, is not static. Gluons fluctuate in a collective
fashion, illustrated by the red-orange-yellow-green-blue fluid. Sometimes the gluon field produces extra
quark-antiquark pairs; here, a proton (uud) has fluctuated into a ? hyperon (uds) and a kaon (u).
CREDIT: D. LEINWEBER/CENTRE FOR THE SUBATOMIC STRUCTURE OF MATTER, UNIVERSITY OF
ADELAIDE
|
>
| Fun with Probability |
|
It is not always easy to grasp the concepts and implications
of probabilty theory. For example, a problem in probability
called the "Monty Hall" problem illustratates some of the
difficulty. The problem goes like this:
Based on the the old TV show "let's make a deal" hosted by Monty Hall - there are three doors , two of which contain a zonk and one contains a prize. The contestant is asked to choose a door. Then Monty reveals what's behind one of the other doors ( he shows the one containing the zonk). So with one door revealed ( a zonk) that leaves two closed doors - the one picked by the contestant and the other door. Now Monty asks the contestant - "do you want to switch the door you picked with the other closed door?" Well, what is the best strategy for the contestant? Initially, it looks like it shouldn't make a difference - that is, with only two doors left it would appear the contestant would have a fifty-fifty chance of being correct. Well, wrong!! His best strategy would be to switch doors to win the prize. And why is that? Well, it all boils down to a change in information. At first, there were three doors and the chance of picking the prize is 1/3 but it also means that the chance of being wrong is 2/3. So 2/3 's of the time he will be wrong - thus with this new information, ie, he has a door that has a 2/3 chance of being wrong, then the best strategy would be to switch doors. |
| Not Convinced - Try it a few hundered thousand times |
|
Enter the number of trials and the number of doors and click
run to see the effect of switching or not switching doors.
The simulation run by this window randomly selects which door
wins and randomly selects the player's ( Alice or Bob )
initial choice. Monty Hall then opens one of the remaining
doors which is a loser. Then Alice always stays
with her original door and Bob always switches.
|
| If you want some more on probability - click HERE |
>
| Fun with Cryptology |
|
What is cryptology? First of all cryptology is the science
of cryptography ( codemaking) and cryptanalysis (codebreaking).
We will examine cryptography and try to understand how it
works, since we see it all the time when we send an encrypted
message. To a cryptologist, codes and ciphers are two
different concepts. Codes refer to substitutions for letters,
words, or phrases and a cipher is an algorithm to transform
a message into a meaningless jumble. Most of these algorithms
use the concept of a key - which is used in the algorithm to
produce the jumbled message. For example, if we want to
send a message that says "attack" that is encrypted, we could
assign a number to each letter - ie, a=1, t=20, c=3, and k=11.
Thus the message could be sent as 1 20 20 1 3 11 Well, this is not very secure as it is easy to figure out with very little effort, what the message is. So, the next step would be to use a key to further encrypt this message. Okay so let's pick a key that is equal to 5. Now the message becomes: 5 100 100 5 15 55 which also is not secure as it obvious the numbers are all divisible by the same number ie, 5. Now what do we have to do - to send a secure message. We would need a not so obvious key to encipher the message and another key to decipher the message. Fortunately, there is such a method. It is called public key encryption. There are two components to pubic key encryption - a public key and a private key. The public key is used to encrypt ( encipher ) the message and the private key is used to decrypt ( decipher) the message. The public key is available to anyone who wants to send an encrypted message but we want the private key to be known only by the recipient of the message. We obviously don't want to send the private key along with the message, as it may be intercepted and used to decipher the message. The problem is, how do we reduce the exposure of the private key to zero. This is not a simple problem but some very clever people came up with the solution, it is called RSA encryption. Named after the people who invented it ( Rivest, Shamir, and Adleman). How does this work? Let's assume Mary wants Bill to send her a secret message. She would need to generate two keys - public and private. She puts the public key on her website for anybody to read. Bill uses this public key to encipher his message and sends it to Mary. She uses her private key to decipher the message. This was all done without having to send a private key along with the message. So this is secure as long as the public and private keys are not breakable. To ensure this to be the case - the algorithm incorporates a method using 2 really big prime numbers to generate both keys. In fact, it is the product of the 2 big prime numbers that is actually used, the product in fact is a really huge number. This huge number is actually used to generate the keys and it's unbreakability is based on the fact that it is extremely difficult to take a huge number and find its two prime factors. For example, the largest number yet factored is 155 digits long and it took about 300 computers ( fast workstations) more than seven months to get the two prime factors. Well, this all sounds good but what about the details - show me an example of the algorithm to encrypt and decrypt a message. Okay, if you think you have seen enough you can skip the gory details otherwise you can go HERE to see the inner workings of the algorithm. OR - Play with factors - below: |
> Click on sardine pig - for my take on morons

>
|
Everyone is familiar with big AL's formula equating energy and mass - but where did it come from? Einstein's derivation is a bit tricky to grasp - but here is a derivation he perfomed later that really only used simple principles and mathematics. Check it out HERE. |
>
>






